On September 19, 2024, the landscape of cryptocurrency enforcement shifted dramatically. The Bundeskriminalamt, or BKA, which is Germany's Federal Criminal Police Office responsible for combating serious and organized crime, executed a massive takedown known as Operation Final Exchange. This operation targeted 47 Russian-language cryptocurrency exchanges that operated without Know Your Customer (KYC) verification protocols. These platforms were not just random sites; they were critical infrastructure for sanctions evasion, money laundering, and cybercrime. The BKA didn't just shut them down-they seized development servers, production servers, and backup systems, securing over 8 terabytes of data including user registration details, transaction records, and IP addresses.
This wasn't a standard regulatory fine or a warning letter. It was a coordinated strike against financial crime networks that had been exploiting gaps in global oversight. If you have ever wondered how law enforcement tracks digital assets across borders, this operation serves as a textbook example. It highlights the growing sophistication of agencies like the BKA and their ability to dismantle anonymous financial infrastructures that facilitate illicit activities ranging from ransomware payments to darknet drug sales.
The Anatomy of Operation Final Exchange
To understand the scale of this event, we need to look at what exactly was targeted. The 47 exchanges involved were primarily instant-swap services catering to Russian-speaking users. Unlike major regulated exchanges such as Coinbase or Binance, these platforms required no identification. Users could swap cryptocurrencies or convert fiat currency without providing names, phone numbers, or even email addresses. This lack of KYC compliance made them attractive to criminals seeking anonymity but also created significant risks for legitimate users who might inadvertently interact with sanctioned entities.
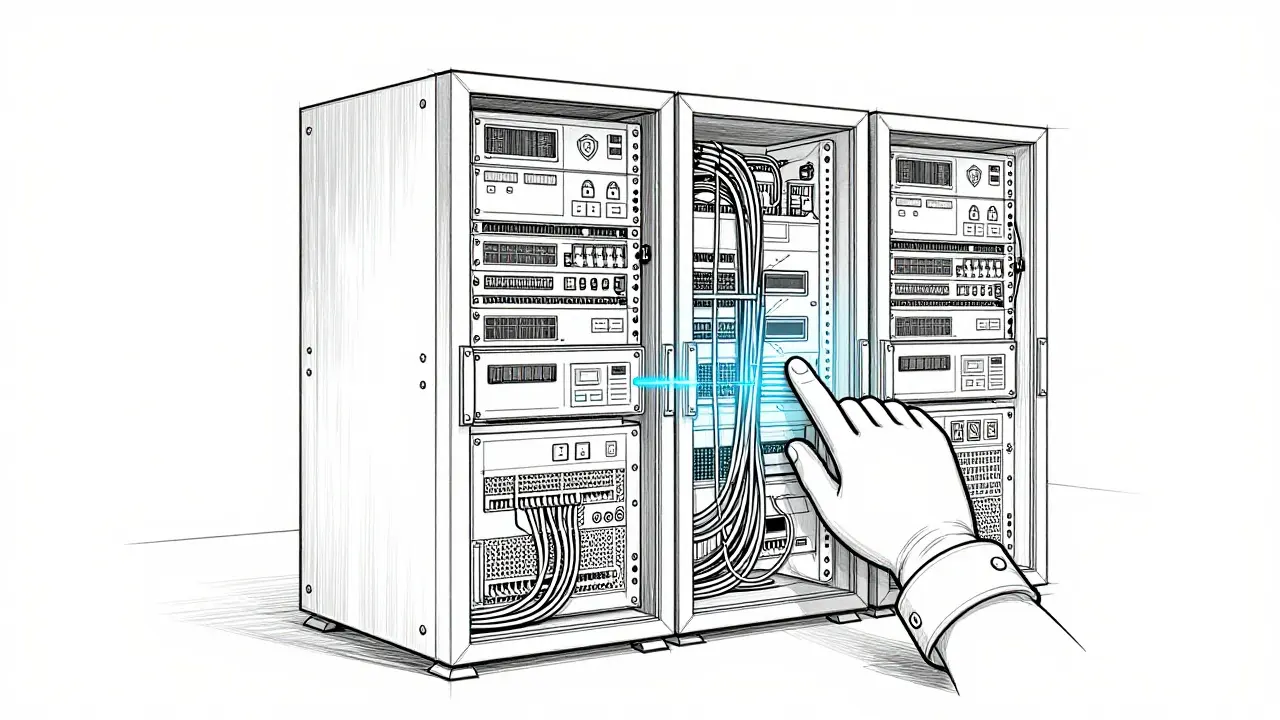
The technical execution was precise. Authorities didn't just take down the live websites. They secured the entire backend infrastructure. This included:
- Production Servers: The active systems handling daily transactions.
- Development Servers: Systems used by operators to update code and features.
- Backup Systems: Redundant storage ensuring data preservation even if primary systems failed.
By seizing all three layers, the BKA prevented operators from simply migrating to new hosting providers or restoring services from backups. This comprehensive approach disrupted operations far more effectively than traditional shutdowns, where criminal groups often bounce back within days. The message sent to users was clear: "We have found their servers and seized them... We have their data - and therefore we have your data." This psychological component added pressure, signaling that investigations would continue based on the recovered evidence.
Why Target No-KYC Exchanges?
You might ask why focus specifically on no-KYC platforms. The answer lies in their role in facilitating sanctions evasion. These exchanges provided direct on-ramping and off-ramping services for sanctioned Russian banks, creating systematic channels for bypassing international restrictions imposed following geopolitical conflicts. Without KYC checks, there was no way to verify if a user was located in a sanctioned jurisdiction or if funds originated from prohibited sources.
Cybercriminals relied heavily on these services. Ransomware groups, botnet operators, and darknet marketplace vendors needed ways to launder proceeds quickly while maintaining plausible deniability. Instant-swap exchanges allowed them to move funds through multiple cryptocurrencies, obscuring the trail. According to Chainalysis, a leading blockchain analytics firm, these platforms play a central role in facilitating on-chain cybercrime by enabling rapid obfuscation of fund origins.
However, it wasn't just about high-profile crimes. Everyday users engaging in privacy-focused transactions also utilized these services. While some argued that targeting them infringed on legitimate privacy rights, regulators viewed the absence of basic compliance controls as unacceptable risk. The decision reflects a broader trend where governments prioritize security and anti-money laundering efforts over absolute financial anonymity.
Comparison with Previous Enforcement Actions
How does Operation Final Exchange compare to other notable crackdowns? Let's look at some key metrics alongside previous operations like the ChipMixer seizure.
| Operation Name | Year | Target Type | Data Seized | Key Outcome |
|---|---|---|---|---|
| Operation Final Exchange | 2024 | No-KYC Exchanges | 8+ TB | Disrupted 47 platforms simultaneously |
| ChipMixer Seizure | 2023 | Mixing Service | €90M laundered | Shut down major mixing service |
| Hive Darknet Market | 2020 | Darknet Marketplace | Varies | Arrested administrators |
What sets Operation Final Exchange apart is its scope and methodology. While ChipMixer focused on a single mixing service processing millions in illicit funds, Final Exchange hit 47 distinct entities. More importantly, it targeted the underlying infrastructure rather than just the front-end interfaces. This multi-server seizure strategy ensures that even if operators attempt to rebuild, they lose critical historical data needed to re-establish trust among users.
Additionally, the operation demonstrated advanced coordination between domestic and international partners. The BKA worked closely with Frankfurt's Public Prosecutor's Office and likely collaborated with agencies in other jurisdictions given the cross-border nature of cryptocurrency flows. Such cooperation is essential when dealing with decentralized networks that don't respect national boundaries.
User Reactions and Community Impact
The immediate reaction across cryptocurrency communities was mixed. On forums like Reddit's r/cryptocurrency, many expressed concern about expanded surveillance capabilities. Privacy advocates worried that legitimate users seeking financial independence might face unintended consequences due to association with seized platforms. Others pointed out that using no-KYC services inherently carries higher risk, especially when those services cater explicitly to illicit activities.
In Russian-language communities, panic spread rapidly. Users reported fears about potential prosecution based on seized transaction data. Telegram channels dedicated to cryptocurrency privacy saw decreased activity as members scrambled to find alternative methods for moving funds. Meanwhile, compliance-focused users generally supported the action, viewing it as necessary for legitimizing the industry and encouraging mainstream adoption.
Trust scores for privacy-focused exchanges dropped significantly following the announcement. Platforms listed on aggregators like CoinGecko experienced declines in ratings as investors reassessed risks associated with unregulated services. This shift underscores how enforcement actions can influence market sentiment beyond immediate targets.

Implications for Future Compliance
So what does this mean for you if you're involved in cryptocurrency? First, recognize that anonymity comes at a cost. Services operating without KYC requirements are increasingly vulnerable to takedowns. Regulators worldwide are tightening scrutiny around digital asset providers, particularly those facilitating cross-border transactions.
If you rely on privacy features, consider whether your needs align with legal frameworks in your jurisdiction. Some countries allow certain forms of self-custody solutions while prohibiting others. Understanding local regulations helps mitigate exposure to sudden disruptions like Operation Final Exchange.
For businesses interacting with cryptocurrencies, enhanced due diligence becomes crucial. Partnering with compliant exchanges reduces liability risks and builds credibility with customers and regulators alike. Implementing robust internal controls around virtual asset transfers demonstrates commitment to ethical practices.
Looking ahead, expect similar coordinated efforts to increase in frequency. Law enforcement agencies continue developing technical expertise in blockchain tracing and server seizure operations. Blockchain analytics tools will become even more integral to identifying suspicious patterns early before they escalate into larger issues.
Lessons Learned for Industry Stakeholders
Several key lessons emerge from Operation Final Exchange:
- Infrastructure Resilience Matters: Operators relying solely on frontend protections leave themselves exposed to backend seizures.
- Data Preservation Is Critical: Securing comprehensive datasets enables deeper investigations post-takedown.
- International Cooperation Enhances Effectiveness: Cross-jurisdictional collaboration amplifies impact against global threats.
- User Awareness Drives Change: Educating consumers about risks associated with non-compliant services fosters healthier ecosystems.
These insights apply not only to exchange operators but also developers building wallet software, analysts tracking illicit flows, and policymakers shaping future legislation. Each stakeholder plays a part in determining how effectively society balances innovation with responsibility.
What exactly was Operation Final Exchange?
Operation Final Exchange was a major enforcement action conducted by Germany's Federal Criminal Police (BKA) on September 19, 2024. It involved the simultaneous seizure of 47 Russian-language no-KYC cryptocurrency exchanges along with their complete server infrastructure, including development, production, and backup systems. Over 8 terabytes of data containing user information and transaction records were secured.
Why did authorities target no-KYC exchanges specifically?
No-KYC exchanges were targeted because they facilitated sanctions evasion, money laundering, and cybercrime by allowing users to transact without identity verification. These platforms provided direct access to sanctioned Russian banks and enabled criminals to launder proceeds from ransomware attacks and darknet sales anonymously.
How does this operation differ from previous crackdowns?
Unlike earlier operations focusing on individual services, Operation Final Exchange targeted 47 platforms simultaneously and seized all backend infrastructure-including development and backup servers-preventing rapid restoration. Its comprehensive data collection approach allowed for deeper subsequent investigations compared to simpler shutdowns.
Will my personal data be affected if I used one of these exchanges?
If you used any of the seized exchanges, your transaction history, IP addresses, and registration details may now be accessible to investigators. Whether this leads to further action depends on whether your activities violated laws related to sanctions evasion or money laundering. Consult legal counsel if concerned.
What should regular crypto users do after hearing about this?
Regular users should assess their reliance on unregulated services and consider transitioning to compliant exchanges offering stronger consumer protections. Stay informed about evolving regulations in your region and ensure your own practices adhere to applicable laws regarding virtual asset usage.