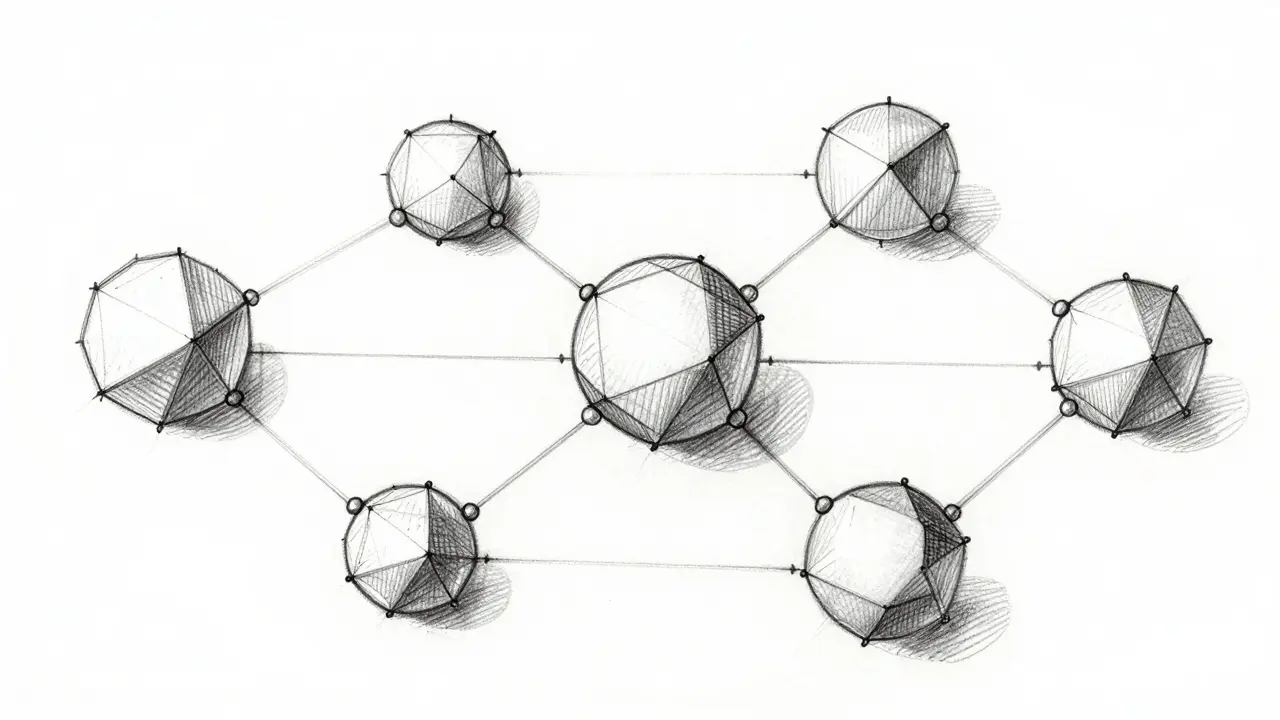
The Trust Problem in Distributed Networks
Imagine you are trying to coordinate a group attack, but some of your generals might be traitors. You don't know who they are, and the messengers carrying orders between you could be intercepted or forged. This scenario describes the famous "Byzantine Generals' Problem," a thought experiment created in the late 1970s to highlight a massive flaw in distributed computing. If computers cannot agree on a single truth because some of them are broken or lying, the whole system collapses.
This isn't just a theoretical puzzle anymore. In our world today, we rely on networks where no one trusts the central server to tell the truth. A blockchainis a distributed ledger technology that records transactions across many computers faces this exact dilemma every second. If one node lies about sending you 5 coins while actually keeping them, does the rest of the network see it? Without a way to stop bad actors, digital money becomes impossible. That is why understanding Byzantine Fault Tolerance is critical for anyone working with decentralized systems.
The core idea is simple: you need a voting system that works even if a portion of the voters are enemies. The math behind this dictates that for a network to remain secure, honest nodes must outnumber malicious ones. Specifically, in most algorithms, you need at least two-thirds of the participants to behave correctly. If more than one-third are corrupted, the system enters a state of ambiguity, and safety guarantees vanish.
Why Traditional Systems Fail Here
In standard computer architecture, if a server crashes, we reboot it. If a drive fails, we swap it out. These are failures of hardware or software bugs, which are predictable. We call these "crash faults." However, a Byzantine failureoccurs when a system component behaves arbitrarily or maliciously, sending conflicting information to different parts of the network is much harder to handle.
Picture a database syncing across three servers. Server A says the balance is $100. Server B says it's $200. Server C says it's $150. Which number is right? In a centralized bank, the bank decides. In a blockchain, there is no boss. The network must decide for itself using cryptography and game theory. If we rely on majority voting alone, a sophisticated attacker could manipulate the vote by creating thousands of fake identities (a Sybil attack). Therefore, real-world BFT algorithms add layers of economic or computational cost to make cheating expensive.
Proof-of-Work as a Byzantine Solution
When Bitcoin launched over a decade ago, it didn't use traditional voting. Instead, it introduced Proof-of-Worka consensus mechanism requiring miners to solve complex mathematical puzzles to validate transactions. While often misunderstood as just "mining," PoW is fundamentally a BFT algorithm. It solves the trust problem by replacing identity-based voting with energy expenditure.
Here is how it achieves fault tolerance. To control the network and double-spend coins, an attacker would need to overpower the entire chain. They would need to solve the cryptographic hash puzzles faster than everyone else combined. This requires controlling more than 51% of the global computing power (hashrate). If a mining pool tries to cheat, they risk devaluing the currency they hold. Thus, the network reaches consensus because attacking the chain becomes economically irrational. Honest nodes simply adopt the longest chain-the one with the most accumulated work-ignoring any divergent blocks sent by bad actors.
This mechanism provides probabilistic finality. When you receive a transaction confirmation, it is likely safe. After six confirmations, the probability of a reversal drops to near zero. However, it lacks immediate certainty. A block could theoretically be orphaned if a longer chain is found later. While robust, the heavy energy requirements eventually pushed the industry toward more efficient solutions as the market matured.
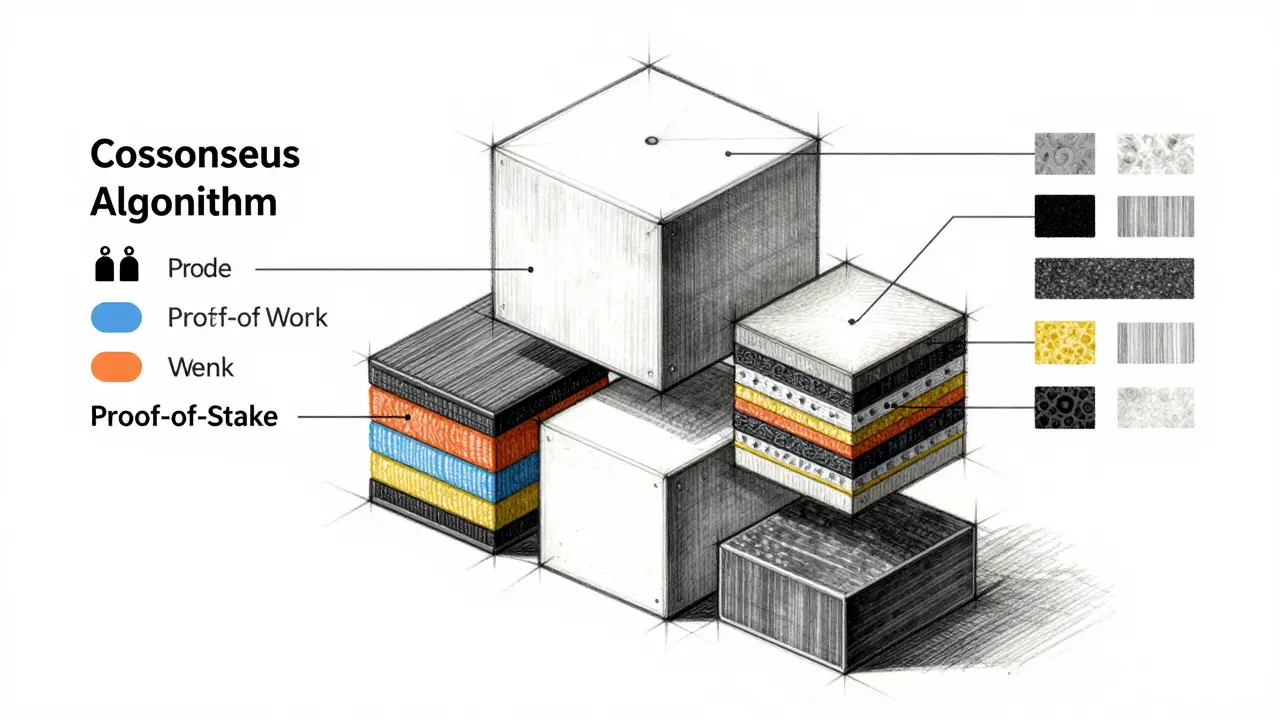
The Shift to Proof-of-Stake
As the industry evolved, Proof-of-Stakea consensus protocol where validators lock up cryptocurrency to create and verify blocks emerged as the leading alternative for general-purpose ledgers. Unlike PoW, which relies on electricity, PoS relies on financial ownership. To become a validator capable of proposing blocks, you must stake a significant amount of the network's native token.
This setup creates a powerful BFT guarantee called "economic slaying." If you are chosen to propose a block but you try to cheat-for example, by submitting invalid transactions or censoring users-you get slashed. Slashing means losing your staked funds permanently. Since validators have skin in the game, honesty becomes the mathematically optimal strategy. On major networks like Ethereum, you need to stake 32 ETH (approximately tens of thousands of dollars in value) to run a full validator. This high barrier prevents the average attacker from easily joining the network.
One nuance to remember: PoS is also subject to the "Nothing at Stake" problem in early designs, where validators could cheaply sign multiple forks. Modern implementations solve this by implementing checkpoints. Once a decision is finalized through a quorum of votes, it cannot be undone. This brings us closer to the concept of absolute finality that older banking systems were used to, moving away from the probabilistic nature of Bitcoin's approach.
Practical Byzantine Fault Tolerance (PBFT)
While PoW and PoS dominate public blockchains, enterprise solutions and privacy-focused chains often use something different called Practical Byzantine Fault Tolerancea consensus algorithm designed for high throughput and low latency in known-node networks. Developed in 1999, PBFT assumes you know who the nodes are ahead of time. This makes it perfect for consortium chains where a group of companies manages the network together.
PBFT operates in distinct phases rather than continuous hashing or slotting. It follows a strict round-robin communication flow:
- Pre-Prepare: A primary node proposes a transaction order.
- Prepare: All other nodes check the proposal and broadcast a "prepare" message if they agree it is valid.
- Commit: Once enough "prepare" messages are collected, nodes broadcast a "commit" message.
- Reply: Clients receive the response once the commit threshold is met.
This process ensures immediate finality. Once a block is committed, it cannot change. There is no chain reorganization. This speed allows PBFT networks to process thousands of transactions per second, far exceeding the limits of PoW. However, this efficiency comes at a cost. The communication overhead is massive. In a network of N nodes, every node must talk to every other node. As you add more nodes, the bandwidth required grows exponentially (quadratic scaling). This is why PBFT doesn't scale well to a global, permissionless internet with millions of strangers participating.
| Mechanism | Security Basis | Finality Type | Energy Cost |
|---|---|---|---|
| Proof-of-Work | Energetic Work | Probabilistic | High |
| Proof-of-Stake | Financial Stake | Deterministic (Eventual) | Low |
| PBFT | Cryptographic Voting | Instant | Network Bandwidth |

Modern Variants and Layered Approaches
The field hasn't stopped at the classics. By 2026, we see advanced versions of these protocols addressing specific weaknesses. Protocols like HotStuff optimize PBFT by reducing the communication rounds needed for consensus. Instead of talking to everyone multiple times, leader-based rotation allows for faster block production while maintaining Byzantine safety.
We also see hybrid approaches. Some Layer 1 blockchains use a combination of PoS for broad security and PBFT-like committees for instant finality. This allows them to claim both the decentralization of open mining/staking and the speed of enterprise-grade databases. These innovations address the fundamental trilemma: the difficulty of balancing security, scalability, and decentralization simultaneously. You generally have to pick two, though newer architectures push the boundaries of that limit.
Another critical aspect involves cross-chain security. As assets move between different networks (like bridging tokens from Chain A to Chain B), verifying that a state change happened without trusting the bridge provider relies on light clients. These light clients are essentially tiny BFT verifiers that check signatures to ensure a block was validly produced on the source chain before allowing an asset transfer. This dependency chain makes understanding these root algorithms crucial for systemic stability.
Limitations of Current Architectures
Despite their sophistication, no algorithm is magic. The biggest remaining weakness in many BFT systems is network partition. If the internet goes down and half the nodes lose connection, the network often stops making progress to prevent errors. Safety is prioritized over liveness. In finance, this pause is usually acceptable; you'd rather not settle a trade than settle the wrong one.
Governance is another soft spot. Even if the code perfectly enforces rules, the upgrade path for the protocol often relies on social consensus. Hard forks happen when the community cannot agree on the BFT parameters or rules. While not a technical flaw in the math, this human element remains a potential point of failure for blockchain ecosystems. Code may guarantee logic, but people manage the deployment.
Frequently Asked Questions
What exactly is a Byzantine failure?
A Byzantine failure occurs when a node in a distributed system behaves unpredictably or maliciously, such as sending conflicting messages to different peers. Unlike a simple crash, the node acts like a traitor, confusing the network.
Does Proof-of-Work provide true BFT?
Yes, Proof-of-Work is considered a Byzantine Fault Tolerant algorithm. It tolerates bad actors by making it too expensive (in terms of electricity and hardware) to overpower the honest network majority.
Is PBFT suitable for public blockchains?
Generally, no. PBFT requires a fixed set of known validators and suffers from high communication overhead as the network grows. It works best for private or consortium chains with limited nodes.
Can BFT algorithms be hacked?
Mathematically, BFT holds as long as honest nodes are the majority. However, implementation bugs, smart contract vulnerabilities, or external governance attacks can still compromise the system, even if the core consensus math remains intact.
What happens during a 51% attack?
If an attacker gains more than 50% of the hash rate (in PoW) or stake (in PoS), they can potentially rewrite history and double-spend. However, they still cannot forge arbitrary transactions due to cryptographic signatures.